Month: December 2022
When the year is coming to a close, it’s the perfect time to plan for the future. Most businesses begin the year with the hope of growing and improving operations. Much of how a business operates depends on technology. So, it makes sense to look to your IT for areas of optimization.
A year-end technology review provides an opportunity to look at several areas of your IT. The goal is to take time to focus on improvements you can make to boost your bottom line. As well as what tactics to take to reduce the risk of a costly cyberattack.
A recent study by Deloitte looked at digitally advanced small businesses. Small businesses that make smart use of technology are well ahead of their peers. Here are some of the ways they excel:
- Earn 2x more revenue per employee
- Experience year-over-year revenue growth nearly 4x as high
- Had an average employee growth rate over 6x as high
The bottom line is that companies that use technology well, do better. They are also more secure. According to IBM, businesses that have an incident response plan reduce the costs of a data breach by 61%. Using security AI and automation can lower costs by 70%.
This year-end, take some time to do a technology review with your IT team or managed IT provider. This will set you up for success and security in the coming year.
Considerations When Reviewing Your Technology at Year-End
The goal of a year-end technology review is to look at all areas of your IT infrastructure. Security, efficiency, and bottom-line considerations will be the key drivers for future initiatives.
Technology Policies
When technology policies get outdated, people stop following them. Review all your policies to see if any of them need updating to reflect new conditions. For example, if you now have some staff working from home, make sure your device use policy reflects this.
When you update policies, let your employees know. This gives them a refresher on important information. They may have forgotten certain things since onboarding.
Disaster Recovery Planning
When is the last time your company did an incident response drill? Is there a list of steps for employees to follow in the case of a natural disaster or cyberattack?
Take time to look at disaster recovery planning for the new year. You should also put dates in place for preparedness drills and training in the coming months.
IT Issues & Pain Points
You don’t want to go through a big IT upgrade without considering employee pain points. Otherwise, you might miss some golden opportunities to improve staff productivity and well-being.
Survey your employees on how they use technology. Ask questions about their favorite and least favorite apps. Ask what struggles they face. Let them tell you how they feel technology could improve to make their jobs better. This, in turn, benefits your business. It can also help you target the most impactful improvements.
Privileged Access & Orphaned Accounts
Do an audit of your privileged accounts as part of your year-end review. Over time, permissions can be misappropriated. This leaves your network at a higher risk of a major attack.
You should ensure that only those that need them have admin-level permissions. The fewer privileged accounts you have in your business tools, the lower your risk. Compromised privileged accounts password open the door to major damage.
While going through your accounts, also look for orphaned accounts. You need to close these because they’re no longer used. Leaving them active poses a security risk.
IT Upgrade & Transformation Plans for the New Year
If you make IT upgrades and decisions “on the fly” it can come back to bite you. It’s best to plan out a strategy ahead of time, so you can upgrade in an organized way.
Have a vulnerability assessment performed. This gives you a list of potential problems your company should address. Eliminating vulnerabilities improves your cybersecurity. Planning ahead allows you to budget for your upgrades and avoid unplanned expenses.
Cloud Use & Shadow IT
Review your use of cloud applications. Are certain apps hardly used? Do you have redundancies in your cloud environment? A review can help you cut waste and save money.
Also, look for uses of shadow IT by employees. These are cloud applications that are being used for work but did not go through approval. Management may not even be aware of them. Remove this security risk by either closing the accounts or officially approving them.
Customer-Facing Technology
Don’t forget to look at the customer experience of your technology infrastructure. Go through your website and contact process as a customer would.
If you get frustrated by things like site navigation, then your customers and leads may be too. Include optimizations to your customer-facing technology in your new year plans.
Schedule a Technology & Security Assessment Today!
We can help you with a thorough review of your technology environment to give you a roadmap for tomorrow. Contact us today for a free consultation.
This Article has been Republished with Permission from The Technology Press.
It seems that nearly as long as passwords have been around, they’ve been a major source of security concern. Eighty-one percent of security incidents happen due to stolen or weak passwords. Additionally, employees continue to neglect the basics of good cyber hygiene.
For example, 61% of workers use the same password for multiple platforms. And 43% have shared their passwords with others. These factors are why compromised credentials are the main cause of data breaches.
Access and identity management have become a priority for many organizations. This is largely due to the rise of the cloud. As well as the practice of people needing to only enter a username and password to access systems.
Once a cybercriminal gets a hold of an employee’s login, they can access the account and any data that it contains. This is especially problematic when it’s an account like Microsoft 365 or Google Workspace. These accounts can access things like cloud storage and user email.
Below, we’ll explain what conditional access is. As well as how it works with multi-factor authentication (MFA). We’ll also review the advantages of moving to a conditional access process.
What Is Conditional Access?
Conditional access is also known as contextual access. It is a method of controlling user access. You can think of it as several “if/then” statements, meaning “if” this thing is present, “then” do this.
For example, conditional access allows you to set a rule that would state the following. “If a user is logging in from outside the country, require a one-time-passcode.”
Conditional access allows you to add many conditions to the process of user access to a system. It is typically used with MFA. This is to improve access security without unnecessarily inconveniencing users.
Some of the most common contextual factors used include:
- IP address
- Geographic location
- Time of day
- The device used
- Role or group the user belongs to
Conditional access can be set up in Azure Active Directory. It can also be set up in another identity and access management tool. It’s helpful to get the assistance of your IT partner. We can help with setup and the conditions that would make the most sense for your business.
The Benefits of Implementing Conditional Access for Identity Management
Improves Security
Using conditional access improves security. It allows you more flexibility in challenging user legitimacy. It doesn’t just grant access to anyone with a username and password. Instead, the user needs to meet certain requirements.
Contextual access could block any login attempts from countries where no employees are. It could also present an extra verification question when employees use an unrecognized device.
Automates the Access Management Process
Once the if/then statements are set up, the system takes over. It automates the monitoring for contextual factors and takes the appropriate actions. This reduces the burden on administrative IT teams. It also ensures that no one is falling between the cracks.
Automated processes are more accurate and reliable than manual processes. Automation removes the human error component. This helps ensure that each condition is being verified for every single login.
Allows Restriction of Certain Activities
Conditional access isn’t only for keeping unauthorized users out of your accounts. You can use it in other ways. One of these is to restrict the activities that legitimate users can do.
For example, you could restrict access to data or settings based on a user’s role in the system. You can also use conditions in combination. Such as, lowering permissions to view-only. You could trigger this if a user holds a certain role and is logging in from an unknown device.
Improves the User Login Experience
Studies show that as many as 67% of businesses don’t use multi-factor authentication. This is despite the fact that it’s one of the most effective methods to stop credential breaches.
One of the biggest reasons it is not used is because of the inconvenience factor for employees. They may complain that it interferes with productivity. Or say that it makes it harder for them to use their business applications.
Using conditional access with MFA can improve the user experience. For example, you can require MFA only if users are off the premises. You can put in place extra challenge questions on a role or context-based basis. This keeps all users from being inconvenienced.
Enforces the Rule of Least Privilege
Using the rule of least privilege is a security best practice. It means only granting the lowest level of access in a system as necessary for a user to do their work. Once you have roles set up in your identity management system, you can base access on those roles.
Conditional access simplifies the process of restricting access to data or functions. You can base this on job needs. It streamlines identity management. This is because it contains all functions in the same system for access and MFA rules. Everything stays together, making management simpler.
Get Help Implementing Conditional Access Today!
Once conditional access is set up, the automated system takes over. It improves your security and reduces the risk of an account breach. Contact us today for a free consultation to enhance your cybersecurity.
This Article has been Republished with Permission from The Technology Press.
Bring your own device (BYOD) is a concept that took hold after the invention of the smartphone. When phones got smarter, software developers began creating apps for those phones. Over time, mobile device use has overtaken desktop use at work.
According to Microsoft, mobile devices make up about 60% of the endpoints in a company network. They also handle about 80% of the workload. But they’re often neglected when it comes to strong cybersecurity measures.
This is especially true with employee-owned mobile devices. BYOD differs from corporate-owned mobile use programs. Instead of using company tools, employees are using their personal devices for work. Many businesses find this the most economical way to keep their teams productive.
Purchasing phones and wireless plans for staff is often out of reach financially. It can also be a pain for employees to carry around two different devices, personal and work.
It’s estimated that 83% of companies have some type of BYOD policy.
You can run BYOD securely if you have some best practices in place. Too often, business owners don’t even know all the devices that are connecting to business data. Or which ones may have data stored on them.
Here are some tips to overcome the security and challenges of BYOD. These should help you enjoy a win-win situation for employees and the business.
Define Your BYOD Policy
If there are no defined rules for BYOD, then you can’t expect the process to be secure. Employees may leave business data unprotected. Or they may connect to public Wi-Fi and then enter their business email password, exposing it.
If you allow employees to access business data from personal devices, you need a policy. This policy protects the company from unnecessary risk. It can also lay out specifics that reduce potential problems. For example, detailing the compensation for employees that use personal devices for work.
Keep Your Policy “Evergreen”
As soon as a policy gets outdated, it becomes less relevant to employees. Someone may look at your BYOD policy and note that one directive is old. Because of that, they may think they should ignore the entire policy.
Make sure that you keep your BYOD policy “evergreen.” This means updating it regularly if any changes impact those policies.
Use VoIP Apps for Business Calls
Before the pandemic, 65% of employees gave their personal phone numbers to customers. This often happens due to the need to connect with a client when away from an office phone. Clients also may save a personal number for a staff member. For example, when the employee calls the customer from their own device.
Customers having employees’ personal numbers is a problem for everyone. Employees may leave the company, and no longer answer those calls. The customer may not realize why.
You can avoid the issue by using a business VoIP phone system. These services have mobile apps that employees can use. VoIP mobile apps allow employees to make and receive calls through a business number.
Create Restrictions on Saved Company Data
Remote work has exasperated the security issue with BYOD. While BYOD may have meant mobile devices in the past, it now means computers too. Remote employees often will use their own PCs when working outside the office.
No matter what the type of device, you should maintain control of business data. It’s a good idea to restrict the types of data that staff can store on personal devices. You should also ensure that it’s backed up from those devices.
Require Device Updates
When employee devices are not updated or patched, they invite a data breach. Any endpoint connected to your network can enable a breach. This includes those owned by employees.
It can be tricky to ensure that a device owned by an employee is kept updated. Therefore, many businesses turn to endpoint management solutions. An endpoint device manager can push through automated updates. It also allows you to protect business data without intruding on employee privacy.
The monitoring and management capabilities of these tools improve security. This includes the ability to safelist devices. Safelisting can block devices not added to the endpoint manager.
Include BYOD in Your Offboarding Process
If an employee leaves your company, you need to clean their digital trail. Is the employee still receiving work email on their phone? Do they have access to company data through persistent logins? Are any saved company passwords on their device?
These are all questions to ask when offboarding a former staff member. You should also make sure to copy and remove any company files on their personal device. Additionally, ensure that you deauthorize their device(s) from your network.
Let Us Help You Explore Endpoint Security Solutions
We can help you explore solutions to secure a BYOD program. We’ll look at how your company uses personal devices at your business and recommend the best tools. Contact us today for a free consultation.
This Article has been Republished with Permission from The Technology Press.
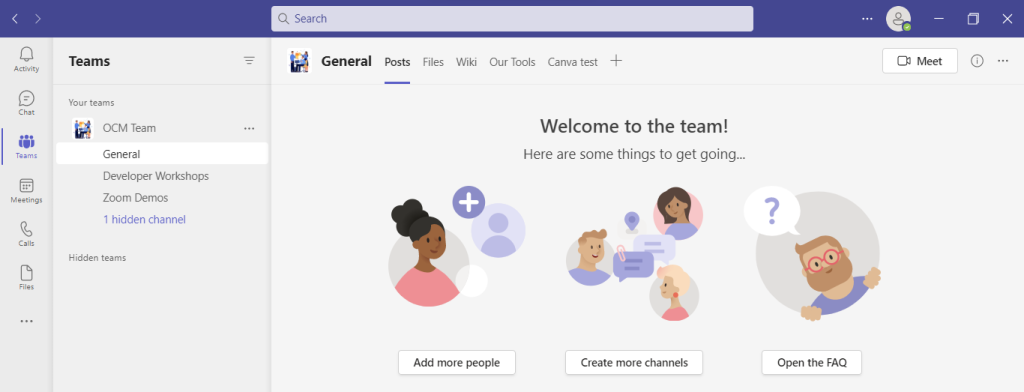
Microsoft Teams is a lot of things. It’s a video conferencing tool, a team messaging channel, and a tool for in-app co-authoring, just to name a few. During the pandemic, the popularity of Teams skyrocketed.
User numbers for MS Teams jumped from 20 million in November 2019 to 75 million in April 2020. As of this year, Microsoft reports a user count of 270 million for the platform. This makes it the most popular business tool for team communications.
But one of the things that makes the app popular is also one that can make the setup complex. Microsoft Teams has many moving parts, but to use them effectively they need to be well organized. Additionally, users need to have a chance to learn the system and train on best practices.
What Can Microsoft Teams Do?
First, let’s look at the different areas of Microsoft Teams and what it can do. Then, we’ll give you a simple setup checklist to help your team get up and running productively.
You can think of Teams as a virtual office in the cloud. It’s a centralized hub where teams can communicate, collaborate, and manage tasks. There is also an external communication component to Teams. You can use the app to video conference with anyone. You can also invite guests to a chat channel.
Here are some of the features of MS Teams:
- Siloed chat channels
- Security for team communications
- Integration with Office apps
- Integration with 3rd party apps
- File sharing
- Video and audio conferencing
- VoIP phone system (with an extra add-on)
- Keep all team resources in a single place
Microsoft Teams Versions
Some good news for small businesses is that there is a free version of Microsoft Teams. If you sign up for a Microsoft 365 business plan, you get the app included, but with a few more features.
Microsoft has also been pushing MS Teams for personal use. So, you can use it to keep your departments better coordinated at work. Or to manage family video calls or PTA meeting collaboration. It’s a versatile and scalable virtual office platform.
Easy Checklist for Setting Up Microsoft Teams
1. Set Up Your Teams/Departments
One of the advantages of Teams is that it allows you to set up specific areas for your groups to collaborate. You do not want everyone to set these teams up on their own, or you could end up with an unorganized mess.
Some ideas for setting these up:
- Set up teams by department (accounting, marketing, etc.)
- Add a company-wide team (where everyone can collaborate)
- Set up teams by role (office managers, executives, etc.)
Typically, if you mirror the hierarchy of your organization, that’s a good place to start. Team areas are secured so only those users invited can see or access any of the content in that team.
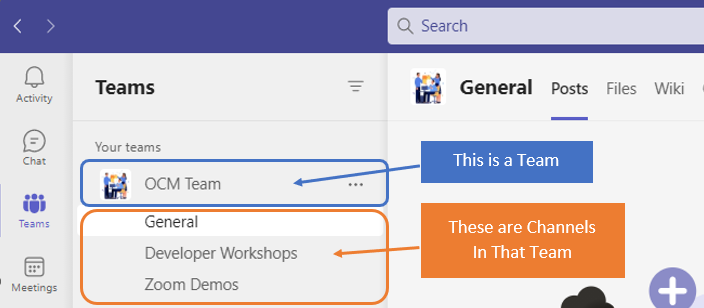
2. Add Team Members
For each team, add the members allowed to take part in that team. These would be people that can see the resources posted in that team area. It would normally be the members of the department or group that the team is designed for.
3. Set Up Team Channels
The next level beneath the Team is the Channels. These team channels help organize conversations. For example, within a team set up for your marketing department, you may decide to add three channels. This keeps conversations more focused and makes it easier to find things.
For instance, you could have channels for:
- Website Management
- Social Media
- Offline Advertising
Team channels are another area that you want to control. Don’t let everyone set up channels without a plan, otherwise, things get messy fast.
4. Set Up Team Tabs
Tabs are a great way to foster productivity. Say that employees on your accounting team need to access a tax reporting website. Inevitably, there can be time wasted asking for that link or a login. This is especially true if someone is filling in for a co-worker.
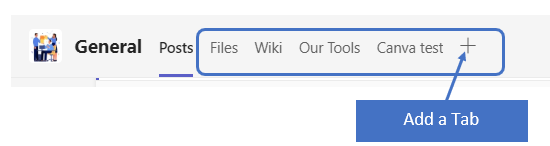
You can add that website link and info to the Tabs area at the top of the team channels. Just click the plus sign to add a new resource and consolidate things for your team members.
5. Schedule MS Teams Training
One of the reasons that company initiatives fail is that users weren’t properly enabled. If users aren’t trained on using MS Teams, then they’ll revert to using whatever they used before. This negates the benefits of moving to Teams when not everyone is onboard.
Work with a Microsoft professional to train your teams. We can provide tips on the most productive features. As well as short-cut their learning curve quite a bit! Make sure to have a realistic timeframe. You should also survey users on whether they feel they need more training.
Need Some Help Implementing Teams in Your Organization?
We can help you over many of the roadblocks that organizations face when starting with Teams. Contact us today for a free consultation to enhance your collaboration and productivity.
This Article has been Republished with Permission from The Technology Press.
Have you ever bought a new computer and then had buyer’s remorse a few months later? Maybe you didn’t pay attention to the storage capacity and ran out of space. Or you may have glossed over memory and experienced constant freeze-ups.
An investment in a new PC isn’t something you want to do lightly. Doing your research ahead of time and consulting with a trusted friend or IT shop can help. It will keep you from making major mistakes that could come back to haunt you later.
Here are several things to consider before you put down your hard-earned money on a new computer.
The Amount of Memory (RAM)
One of the big mistakes that people make when looking for a new computer is to ignore the RAM. Random access memory may be called RAM on the specification or “memory.” If your system has low memory, you run into all sorts of problems.
These issues can include:
- Browser freezing up when you have too many tabs open
- Issues watching videos
- Some software not working properly
- Sluggish behavior
- Inability to open multiple applications
- Constant freezes
Memory is the “thought process” of the PC. If there isn’t enough, it can’t take on another task until it completes the current processing tasks. This can cause frustration and ruin your productivity.
People often go for those low-priced computer deals when looking for a new device. But these can include only 4GB of RAM. That’s not a lot if you do much more than staying in a single application or just a few browser tabs.
The higher the RAM, the more responsive the system performance. So, look for PCs with at least 8GB of RAM. Or higher if you do any graphics/video or other processing-intensive activities.
User Reviews for Longevity
Buying a new computer is an investment. So, it’s natural to want that investment to last as long as possible. You don’t want to spend $700 on a new computer, only to begin experiencing problems when it’s just two years old.
Take your time to research user reviews on the specific models you’re considering. You’ll begin to see patterns emerging. Steer clear of models that have consistent complaints about breakdowns sooner than expected.
You may have to pay a little more for a system that has a better track record of performance. But it will save you in the long run when you have more years of usable life before that device needs replacement.
Whether the PC is for Personal or Business Use
If you have a small business or are a freelancer, you may try to save money by buying a consumer PC. But this could end up costing you more in the long run.
Consumer PCs aren’t designed for continuous “9-to-5” use. They also often lack certain types of firmware security present in business-use models. The price gap has also shortened between good consumer computers and business versions. If you’re not looking at the cheap systems, you’ll find that it’s not that much more to get a business-grade device.
The Processor Used
It can be confusing to read through the processor specifications on a computer. How do you know if Intel Core i7 or i3 is best for your needs? What’s the performance difference between AMD and Intel processors?
If you don’t want to do the research yourself, you could call up your local IT shop. We will be happy to steer you in the right direction. We’ll explain in layman’s terms the differences. As well as which processor makes the most sense for your intended use.
For Laptops: The Case Type
If you’re looking for a laptop computer, it’s important that it is durable. Laptops have some unique characteristics that differ from desktops. For example, the screen is often folded down one or more times per day. Additionally, the keyboard is part of the case and is not easily replaced by the user.
If you get a laptop with a cheap plastic case, it’s bound to break during normal use. Keys could also easily pop off the keyboard, requiring a trip to a computer repair shop.
You want to consider the materials used for the case. Paying an extra $20-$30 upcharge for a better casing is definitely worth it. It can help you avoid unneeded headaches.
Storage Capacity
Storage capacity can be a pain point that you experience after the fact. If you buy a computer without paying attention to hard drive space, you could regret it. You may not be able to transfer over all your “stuff” from the old system.
But storage capacity can also be an area where you can save some money. If you store most of your files in the cloud, then you may not need a lot of hard drive space. The less space you need, the lower the price.
Hard Drive Type
If you can get a computer with a solid-state drive (SSD) rather than a traditional hard disk drive (HDD) you should. SSDs are faster and less likely to have read/write issues. They have no moving parts; thus they are quieter as well.
Solid-state drives have come down in price quite a bit recently. There are many affordable options, and you’ll also find some PCs with both a hard drive and SSD.
Come to Us Before You Spend Money on a New Computer
Don’t blindly invest in a new computer without some expert guidance. Contact us today for a free consultation to save you from a bad new PC experience.
This Article has been Republished with Permission from The Technology Press.
Paying attention to your customer experience directly impacts your bottom line. Companies that are “customer-centric” are 60% more profitable than those that aren’t. In this digital age, customers also expect more from those they do business with.
In today’s world, people can order something on their phones and see it on their doorstep the next day. Keeping up with expectations means leveraging the right technology.
As 2023 is on the horizon, it’s the perfect time to improve your customer experience. Thanks to cloud technology, you don’t have to spend a fortune to do it. Just put in place some of the applications below. These apps focus on making leads and customers happy.
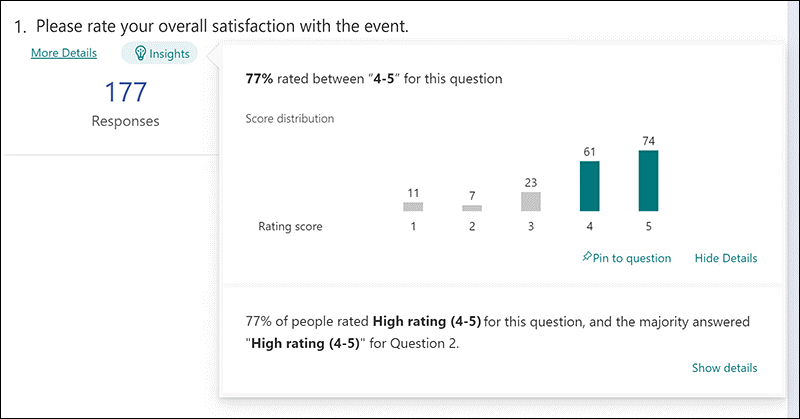
1. Online Survey Application
Doing an annual customer satisfaction survey is a great way to check in with customers. Successful businesses take the feedback they get and use it to make their company better.
But doing these surveys through a Word document attached to an email is so last decade! Use an online survey application to make the process seamless for you and your customers.
Online survey tools are available widely online. If you have Microsoft 365, you’ll find one included. These allow people to fill out surveys on any device and not worry about sending them back in an attachment.
On the receiving end, there is no long process of collating data. Just open your form survey tool and see the results instantly.
2. Smart Chat Bot
Most businesses have a limit on how many hours a day they can pay staff to answer questions. Customer service hours are typically the same as business hours. And staff can get busy, which means answers may take longer to send back to an inquiry.
Putting a smart chatbot on your business website can improve customer satisfaction. It allows people to get an answer right away. They can also get that answer any time of day or night.
68% of consumers like chatbots because they give them fast answers to questions. While they can’t answer every single question, they can handle quite a few. For example, in healthcare and banking, chatbots can take 75-90% of questions.
3. Business Mobile App
People tend to live on their mobile phones these days. They carry them with them everywhere. Mobile apps are often the preferred method of connecting with data and businesses. More Google searches are now done via mobile devices than by desktops.
Think about creating a business mobile app. One that allows customers to connect with you to order products and services. You can use it for customer support, to initiate virtual calls, and more.
4. Facebook Messenger Support
Facebook Messenger is the 2nd most popular iOS app of all time. This Facebook-connected application makes it easy to communicate with friends, family, and companies.
Many businesses now use Messenger to connect with leads and provide customer support. When you use an app that is so popular in this way, you make it easier for customers to reach you. The ability to get a quick answer through Messenger can boost a customer’s opinion of your company.
5. VoIP Phone System with Good Mobile App
When customers must juggle different numbers for your staff, it gets confusing. Should they call your sales rep at their desk line or mobile number? Using a VoIP phone system simplifies the entire process.
Employees can have a single number that they use when at their desks, at their home office, or anywhere. Make sure the VoIP service has a good mobile app. One that is easy for employees to use. This ensures they can easily handle customer calls using their smartphone. It also keeps them from reverting to using their personal number.
6. Text Notification Apps
SMS is becoming the new email for many companies. Retailers like Shoe Carnival and World Market have customers opt-in to text messaging. Customers like this for shipping notifications and to get sale and coupon alerts.
There are several services online that you can use for this purpose. Offering text updates can significantly improve your customers’ experience. Use them for appointment reminders, sale notices, or shipping alerts.
7. All-in-One CRM & Sales Platform
One thing that frustrates customers is a disconnect between sales and support. They may have had a conversation with a salesperson to customize an order. Then, find that customer service knows nothing about it.
To streamline the information flow, look for an all-in-one CRM/Sales platform. These are cloud services that offer a CRM module and a sales module, and both connect. There is a single customer record, so all notes from the sales and customer support side are in the same place. Both teams can view all customer interactions.
This improves the customer experience and results in fewer dropped balls. Efficiency and productivity improve as well because everyone is on the same page.
Get Help with Customer-Facing Technology Support
It’s easy to get lost in a sea of different cloud applications. Let us help you navigate to a better customer experience. Contact us today for a free consultation.
This Article has been Republished with Permission from The Technology Press.